To achieve your clients’ inboxes with e mail advertising and marketing campaigns, your area must be a trusted supply. In any other case, your messages will find yourself hitting the spam folder and stay unnoticed. And e mail authentication helps keep away from this.
So what’s e mail area authentication, why it issues, and what e mail authentication protocols are there? Let’s talk about this.
What’s e mail authentication?
E mail authentication is a apply that suggests validating a sender’s e mail handle to substantiate that it’s approved to ship emails from a selected area. It additionally helps affirm that the area belongs to a sure Mail Switch Agent (MTA) approved to switch an e mail.
(Supply: Selzy)
So, placing it merely, e mail authentication helps affirm that the sender is who they are saying they’re. This validation helps determine spammers and disable them from sending out emails.
Why is it vital?
Having found out what e mail authentication is, let’s dive into why it issues. E mail authentication enhances your area’s safety by confirming to servers that your emails come from a legitimate supply. This, in flip, prevents your model from fraud and impersonation.
Since authentication prevents the malicious exercise out of your area, it will get a trusted status amongst ISPs. This reveals that you’re a dependable and credible sender and, most significantly, preserve your e mail deliverability at degree.
In the long term, area safety and a excessive e mail deliverability charge contribute to the belief in your model and a constructive model picture.
E mail authentication protocols
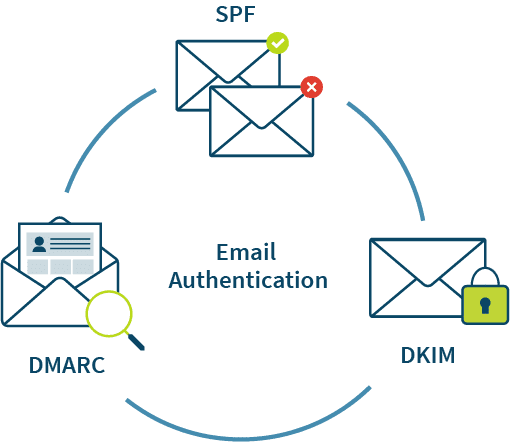
Understanding what e mail sender authentication is just isn’t sufficient — the core of the method lies within the e mail authentication strategies or protocols. These are completely different from e mail protocols, those which can be used for SMTP or IMAP servers.
What’s SMTP server for Gmail?
The Gmail SMTP (Easy Mail Switch Protocol) server is a Google workspace-provided outgoing mail server used to ship messages from a Gmail account. POP (Submit Workplace Protocol) server, for example, permits the consumer to pick out the e-mail and import it to the inbox, making it the incoming server.
It’s essential to configure the Gmail SMTP server settings in your Gmail account to make use of the Gmail SMTP server. The Gmail SMTP server handle, the SMTP username (your Gmail handle), and the SMTP password are all a part of these settings.
With a free Gmail account, you need to use the Gmail SMTP server for 500 emails a day.
Gmail SMTP server protects your e mail messages by utilizing a safe connection. In addition to that, you need to use it to relay messages despatched to your Gmail handle to a different e mail handle or area.
All in all, the Gmail SMTP server is a vital a part of sending emails out of your Gmail account.
Now let’s talk about SPF vs. DKIM vs. DMARC protocols, what they’re, and the way they differ.
(Supply: ZetaGlobal)
SPF report
SPF stands for Sender Coverage Framework and is an inventory of IP addresses inside a site. These addresses are approved and, subsequently, allowed to ship emails. An SPF report is available in a .txt file and is current in a sender’s Area Title System (DNS). SPF is a extensively adopted protocol for e mail authentication.
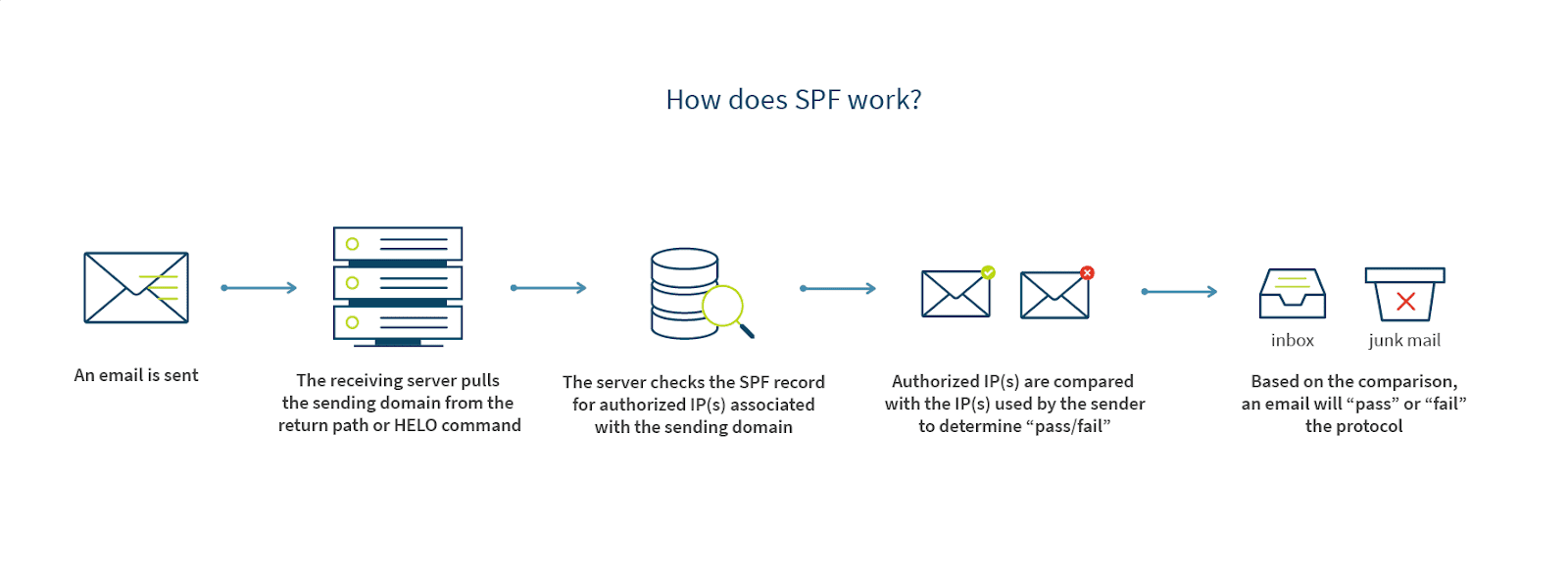
(Supply: ZetaGlobal)
So once you ship an e mail and it reaches the recipient’s server for incoming emails, the SPF e mail authentication runs a verify. It’s a DNS search that goes by all of the SPF information. In case your e mail handle is discovered through the search, then the e-mail proceeds to the recipient’s inbox. In any other case, it’s rejected and won’t be despatched additional.
Finest practices for SPF
SPF has completely different qualifiers — they impart with the server concerning what to do with a selected IP handle. The qualifiers are:
- + — a Cross, that means that the IP handle has handed the check and the e-mail may be accepted;
- – — a Arduous Fail, that means that the IP has failed the check and the e-mail ought to bounce;
- ~ — a Delicate Fail that indicators for a failed check; the e-mail is accepted however marked as failed;
- ? — a Impartial check consequence (not a fail, not a move), and probably, the e-mail is accepted, though it may be rejected.
Whereas these are fairly definitive, the qualifiers are simply strategies on what the server ought to do to an e mail in order that they are often ignored. For instance, an e mail with a Cross could also be despatched to spam, whereas a Arduous Fail one may be accepted.
Normally, the qualifier appropriate for many e mail senders is Delicate Fail. It will ensure all of your emails are despatched however might be marked as “SPF failed” in case they fail. The Impartial coverage is one other frequent selection.
As a result of Delicate Fail accepts all of your emails, you’ll protect your e mail deliverability charge whereas utilizing SPF. On the identical time, you don’t should sacrifice safety as a result of all of the suspicious emails might be marked as such.
DMARC report
DMARC stands for Area-based Message Authentication Reporting and Conformance. This e mail authentication protocol provides area house owners loads of energy over how their failed messages are handled on the recipient’s incoming server.
DMARC supplies a further degree of safety constructed on prime of different protocols, which is known as area alignment. This makes the report extraordinarily efficient in stopping spoofing, impersonating, and different malicious conduct.
DMARC can be mixed with different protocols, guaranteeing most safety. Utilizing a single protocol is inadequate to make sure that all of your emails attain their recipients effectively, and DMARC helps deal with emails that failed SPF or DKIM insurance policies.
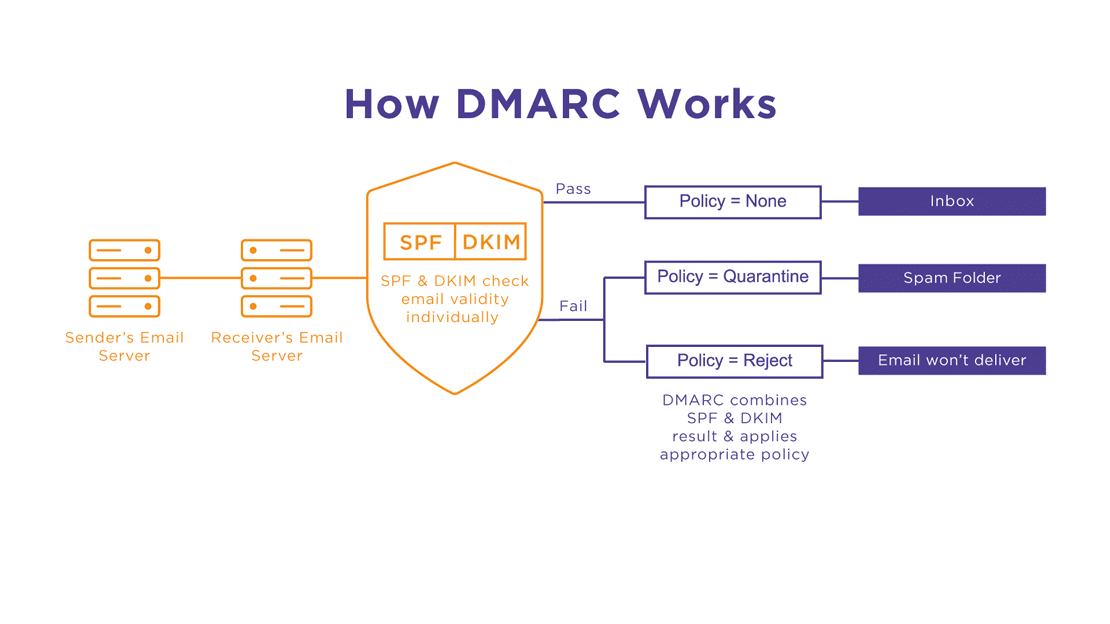
(Supply: Agari)
In addition to the listed capabilities, DMARC additionally permits receiving reviews from the servers in your emails’ efficiency and deliverability. This offers you a chance to determine the the explanation why your emails fail and troubleshoot in time. Finally, DMARC helps preserve a gentle e mail deliverability and builds belief in your model.
Finest practices for DMARC
As already talked about, DMARC permits directing the server concerning what to do with failed emails. Particularly, there are three insurance policies you possibly can select from to determine how one can deal with your failed emails:
- reject — discard emails;
- quarantine — enable emails however ship them to the spam folder;
- none — do nothing.
The final coverage implies that the failed emails are handled as if there was no DMARC arrange. So primarily based on different standards, the e-mail may be accepted, despatched to the spam, or discarded.
Whereas the “None” coverage could appear helpful, it helps with marketing campaign monitoring and report evaluation with out negatively impacting reliable emails and total e mail deliverability. That is additionally the advisable coverage to decide on if you happen to’re beginning with DMARC to get the grasp of the way it works.
Moreover, you possibly can select what share of your failed emails the coverage ought to apply to utilizing the “pct” tag, which might set the remainder of the messages to “None.”
Talking of area alignment, it may be set to “Strict” or “Relaxed.” “Relaxed” is finest if you happen to ship emails by way of exterior companies (an e mail service supplier). As a result of “Strict” area alignment implies that the sending and returning addresses are the identical, DMARC would fail if you happen to ship your emails from a no-reply e mail handle.
DKIM report
DKIM stands for DomainKeys Recognized Mail and is one other customary protocol for e mail authentication, additionally efficient for phishing prevention.
The DKIM report comprises an encryption key and a cryptographic signature which can be used to validate the e-mail handle with a public key on the recipient’s finish. Equally to SPF, the report is saved as a .txt file within the sender’s DNS.
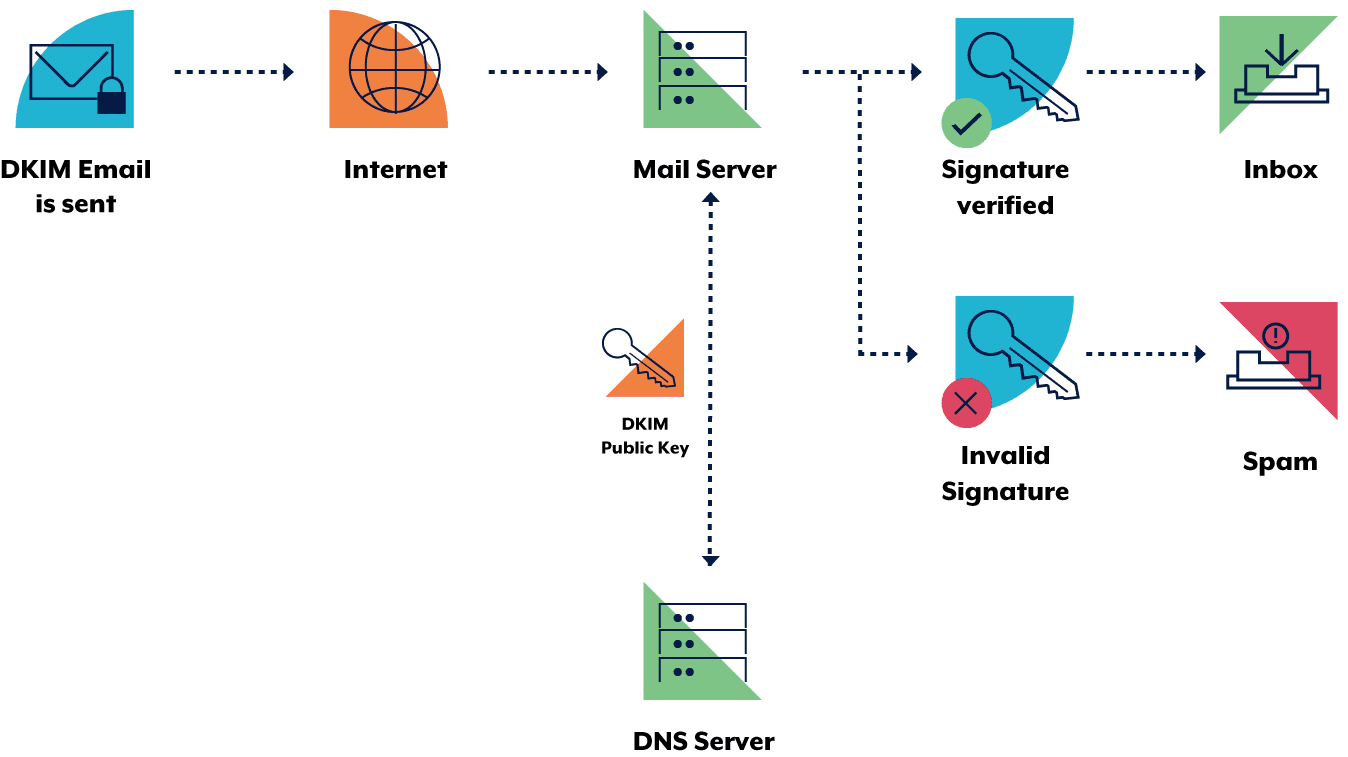
(Supply: Australian Cyber Safety Centre)
The DKIM protocol encrypts a site’s key for e mail authentication in 3 steps:
- The sender creates a DKIM signature by figuring out what fields (i.e., their e mail handle, message physique, and so on.) to incorporate.
- The e-mail system creates a hash string of chosen textual content fields.
- The hash string is encrypted with a personal key that solely the sender can entry.
To authenticate an e mail handle, the server seems to be for a match between the non-public and public keys within the DMS. If there’s one, the DKIM signature may be decrypted again to the hash string, and the e-mail is delivered. And in case there is no such thing as a match, the DKIM check fails, and the e-mail is probably discarded.
Finest practices for DKIM
In addition to the absence of a match between non-public and public keys, DKIM checks can fail for different causes. To keep away from DKIM failures, keep away from instances like the next:
- the fields within the hash string are modified whereas the e-mail is in transit;
- the non-public key size is shorter than 1024 or 2048 bits; another lengths are now not supported;
- the DNS zone of the sender’s area just isn’t accessible for search, which is a frequent challenge with poor internet hosting suppliers.
To maintain the DKIM report safe and efficient, it’s important to run common updates of personal and public keys. By updating your keys a few times a yr, you forestall any dangers of sending out spam out of your area.
When altering the keys, ensure to have two signatures accessible — some emails should still be in transit, and altering each keys with a single signature will result in a DKIM verify failure. However in case you have a number of signatures, one will move even when the opposite fails.
DKIM report can be probably the most appropriate one for e mail auto-forward. If you use ESPs, DKIM doesn’t contemplate it a failure that the sender’s and return e mail addresses differ (like SPF). It’s because the signature is assigned to the e-mail physique, which stays unchanged throughout auto-forward.
Do you have to use all e mail authentication protocols?
After studying what e mail authentication is, you almost certainly now perceive the significance of mixing completely different e mail protocols. DMARC, DKIM, and SPF deal with area authentication in very other ways, which suggests utilizing just one protocol gained’t cowl all of your authentication wants.
So as a result of every protocol runs checks otherwise, utilizing a number of or all three strategies provides the best area safety and e mail deliverability charge.
The way to check e mail authentication?
There are a lot of methods to check your e mail authentication, each manually and routinely. To run a guide verify, ship your check e mail to a Gmail consumer, click on “Extra” on the acquired e mail, and choose “Present authentic.” You will notice a brand new window with SPF, DKIM, and DMARC verify outcomes. If they’re “PASS,” then your area is authenticated.
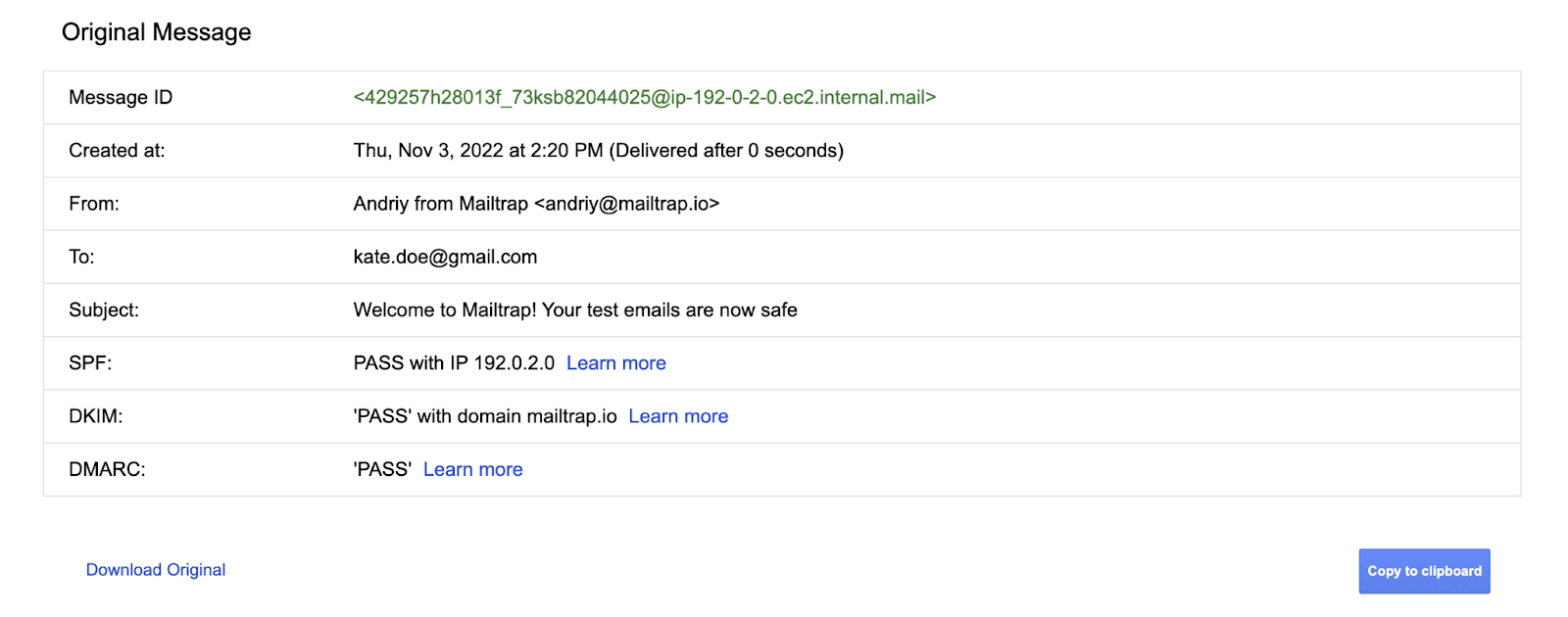
(Supply: Mailtrap)
You can even discover loads of instruments for automated e mail authentication checks, like DMARC Analyzer, which checks for all three protocols, DNS Checker, DKIM Wizard, and different single protocol checkers.
With Postmaster Instruments by Gmail, you possibly can verify your e mail efficiency, determine supply errors, and analyze detailed spam reviews. You might want to have a Google account to trace knowledge and examine a wide range of informative dashboards.
One other software that automates your e mail authentication and runs common checks for you is Mailtrap E mail API. It verifies your area by all three protocols and updates DKIM keys routinely each 4 months. With this software, you possibly can all the time make certain that your area is authenticated.
Wrapping up
E mail authentication is area verification, which confirms its reliability and safety and helps preserve e mail deliverability excessive. Authentication is run utilizing three forms of protocols: SPF, DMARC, and DKIM information. Whereas every protocol can authenticate your area, it’s finest to make use of three information altogether to make sure that your e mail handle is authenticated always.
Be part of Stripo to design lovely emails effortlessly